Screenly offers SAML support with Microsoft Entra ID (formerly Azure Active Directory). Screenly also supports SAML with Okta, which you can learn more about here, and Auth0, which can you find here.
SAML stands for “Security Assertion Markup Language” and allows users to transfer identity information between an identity provider (IdP) and a service provider (SP).
Please see below for more information on how to configure Screenly to work with SAML.
Metadata Location
If this is needed, here are the steps to find your metadata:
Login to your Screenly account (only the account owner can complete this).
Take the first part of the URL showing in your browser - e.g. https://YOUR-DOMAIN-HERE.screenlyapp.com/
Then append “sso/saml_metadata_view” to the end of it - e.g. https://YOUR-DOMAIN-HERE.screenlyapp.com/sso/saml_metadata_view
An example from a test account would look like: https://screenly-testing-inc.screenlyapp.com/sso/saml_metadata_view
This will then bring up a page with your metadata.
Step by step setup with Microsoft Entra ID
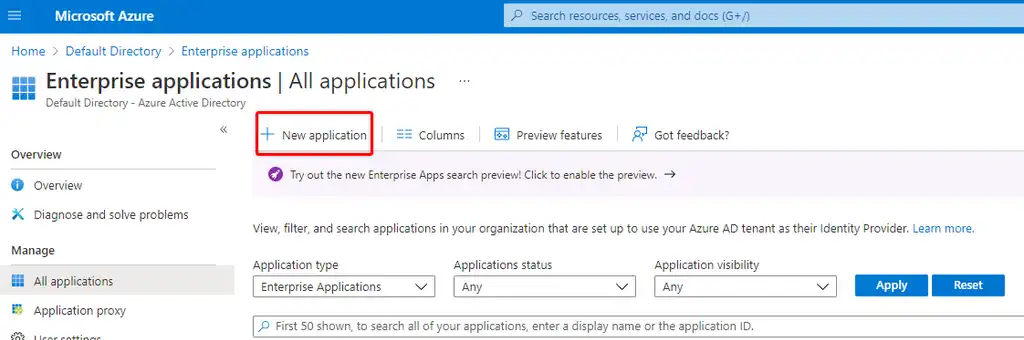
Step 1 — Go to the Microsoft Entra ID console, Enterprise Applications, then click ‘New Application’.
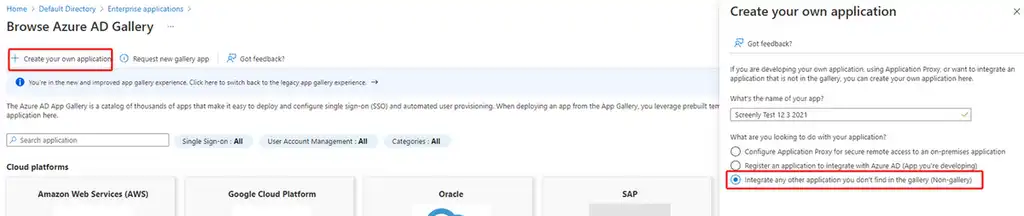
Step 2 — Click on the option to create your own application, name it, and then select the option to “Integrate any other application you don’t find in the gallery (Non-Gallery).
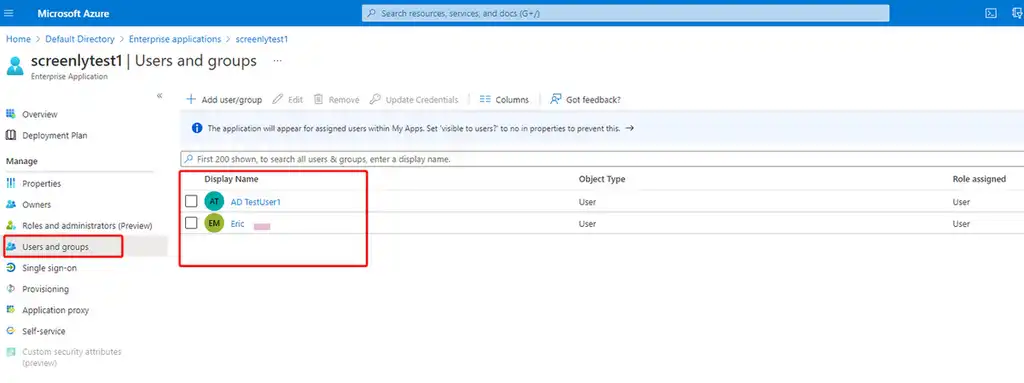
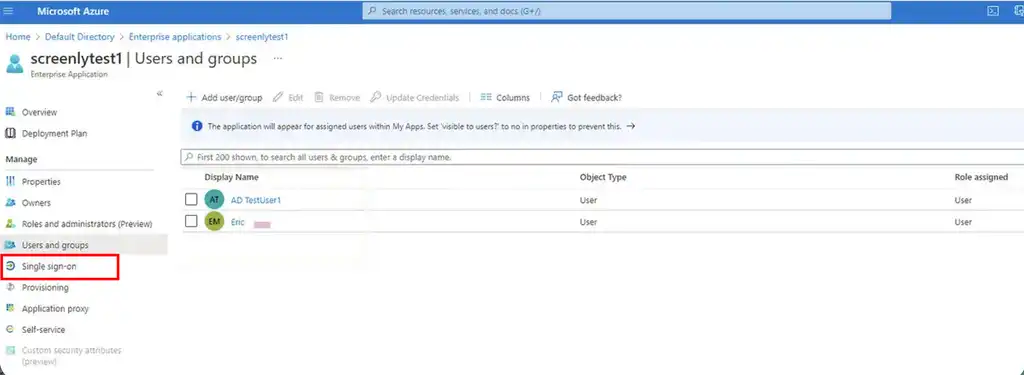
Step 3 — Assign your users and/or groups to the application.
Step 4 — Click on ‘Single-sign-on’ on the left side of the page.
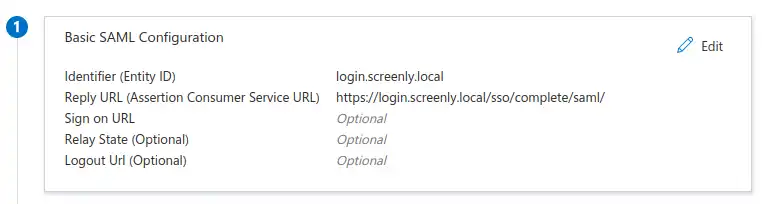
Step 5 — Complete the following settings in the ‘Basic SAML Configuration’ section:
- Identifier (Entity ID) — login.screenlyapp.com
- Reply URL (Assertion Consumer Service URL) — https://login.screenlyapp.com/sso/complete/saml/
- Sign on URL — leave blank
- Relay State — the first part of your Screenly domain when logging into your dashboard. e.g. If your dashboard URL is “https://test-inc.screenlyapp.com/manage/dashboard”, your relay state would be “test-inc”.
- Logout Url — leave blank
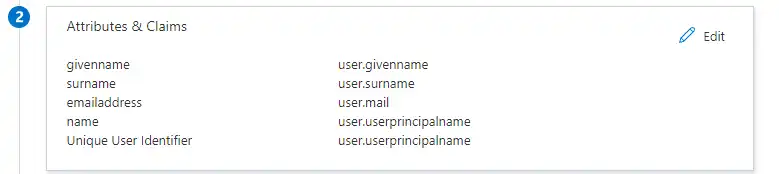
Step 6 — Ensure your settings in the ‘Attributes & Claims’ section match the following:
- givenname — user.givenname
- surname — user.surname
- emailaddress — user.mail
- name — user.userprincipalname
- Unique User Identifier — user.userprincipalname
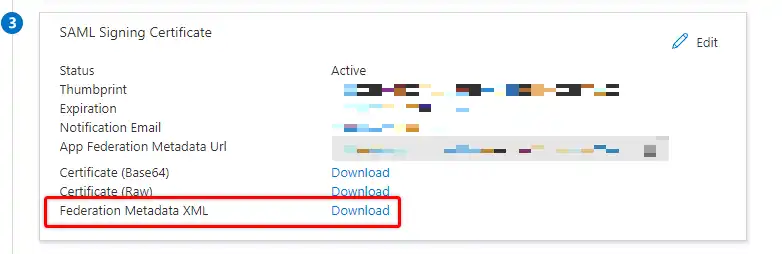
Step 7 — Download and open the ‘Federation Metadata XML’
Step 8 — Log into your Screenly account, and go to the SAML section found in Settings — Security. (Only the account owner can view and edit this setting.)
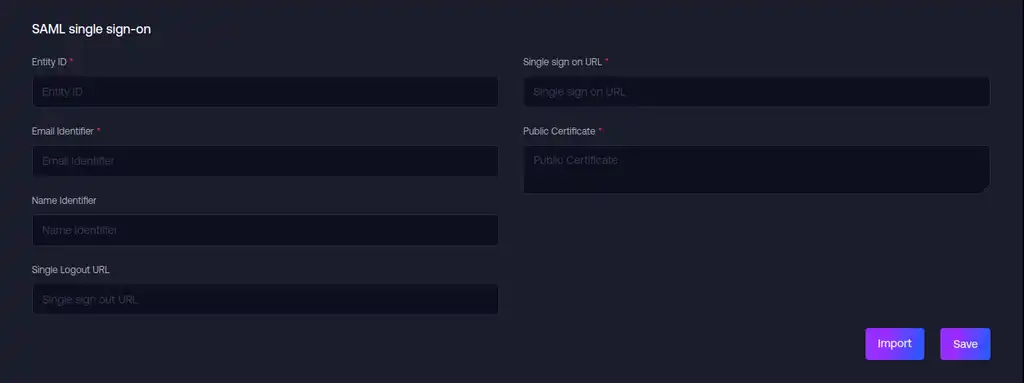
Step 9 — Fill in the fields with the details from your ‘Federation Metadata XML’ file from Step 7 above.
- Entity ID — entityID (get value from the ‘Federation Metadata XML’ file)
- Email Identifier — name_id (use this value)
- Single sign on URL — SingleSignOnService[Location] (get value from the ‘Federation Metadata XML’ file)
- Single Logout URL — SingleLogoutService[Location] (get value from the ‘Federation Metadata XML’ file)
- Name Identifier — http://schemas.microsoft.com/identity/claims/displayname (use this value)
- Public Certificate — X509Certificate (get value from the ‘Federation Metadata XML’ file - remove any BEGIN and END lines from the X.509 certificate when pasting into Screenly, and only paste the content of the certificate).
Step 10 — Save the configuration, and now SAML should be configured. You can test this by clicking the ‘Copy URL’ button below the SAML settings in Screenly, logging out of Screenly, then pasting the URL into the browser to login.
Step 11 — Return Back to Microsoft Entra ID console on Single Sign on section of your application and fill in RelayState (which is required if you want to use IdP-initiated flow). RelayState is the hash that takes from the Screenly SAML URL login (/sso/login/saml?idp=HASH).
That completes the setup.
What is the user authorization process with SAML?
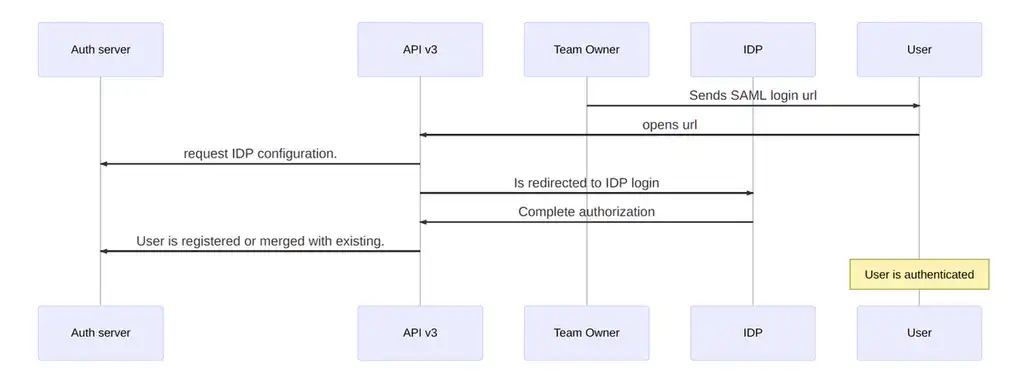
First, the owner sends the SAML login url. This is a necessary step to invite a new user.
Next, the user redirects to the IdP authorization screen.
The next step is for the user to complete authorization. When the user completes IdP authorization, the IdP redirects the user back to Screenly with the IdP’s response.
The user can then register as a new user or, if the user already exists, the user can merge his or her account. This process is the same registration process as SSO.
That’s all for now!